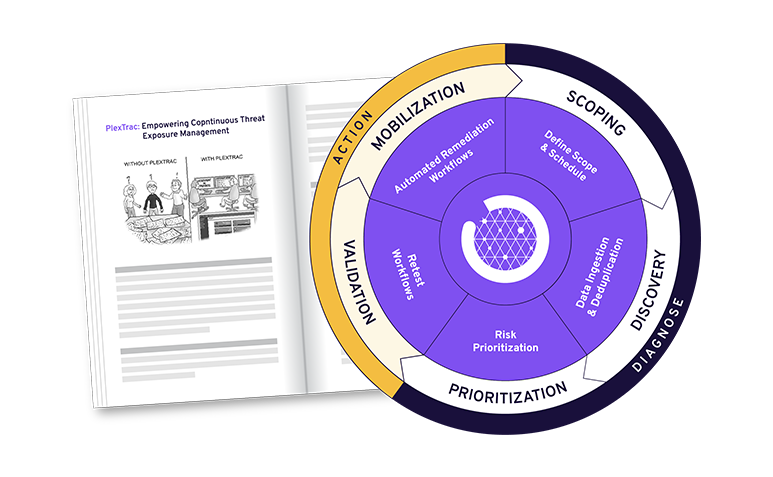
Automating Pentest Delivery: A Step-by-Step Guide
Modernize pentest operations by unifying findings and delivering continuous, actionable results.
Staying ahead of evolving cyberattacks is no small task. While pentesting and vulnerability assessments are essential for identifying and mitigating risks, organizations need to go beyond being merely proactive.
GET YOUR COPY