Remediation and Final Testing Phases: Show Progress, Enhance Security Posture
Hack Your Pentesting Routine
In this series, we’re discussing the ten key phases of a penetration test, talking about the serious pain points in each, and demonstrating how PlexTrac can eliminate these problems.
In this approach, there are 10 phases of the penetration test engagement, each defined by a different group of stakeholders, participants or activities requiring a serious context shift.
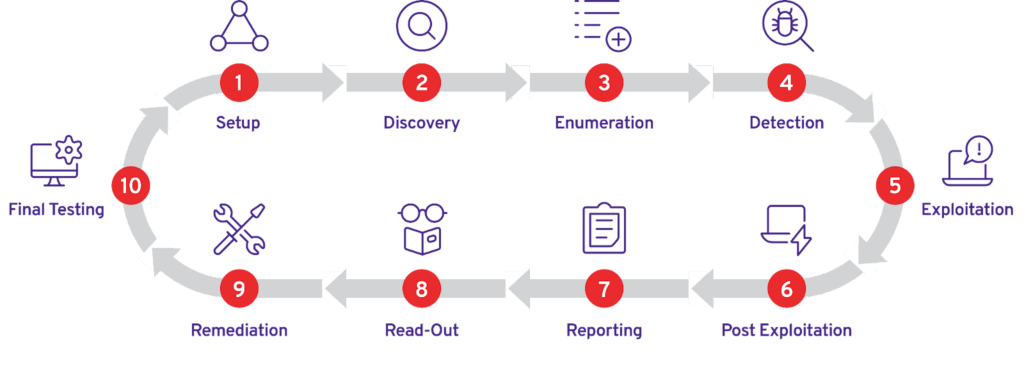
Check out the complete discussion of the pentesting cycle in our “Introducing ALL the Phases of Pentesting” article.
Penetration Testing Phases Nine and Ten
The final phases of the pentest include
- Remediation
- Final Testing (retesting)
The Remediation phase can be handled in varying ways depending on the structure of the organization providing the security assessment and test. Internal teams and service providers have somewhat of an advantage over consultancies, because they will usually have the ability to more closely collaborate with the teams that are remediating, or in other words, fixing the flaws identified during the assessment. Remediation is the primary purpose of a pentest, red team operation, or vulnerability assessment; identifying vulnerabilities is important, but fixing or otherwise mitigating the risks that those flaws present is arguably the most important aspect. Remediation occurs after the results of the tests are handed off. Then the system or application owners go about the task of fixing the flaws.
The Final Testing phase, otherwise known as the “retest” phase, is when the security service providers determine if the remediation activity was successful or not. The flaws previously identified are tested again. Ideally, the flaws have been fixed, the system decommissioned, or the flaw is otherwise unable to be taken advantage of or observed. Sometimes retesting can be cyclic, in that multiple rounds of retesting occur, or based on the results of retesting, more remediation is necessary.
The end result of both of these phases is the security posture for the organization that underwent a security test or assessment is heightened because flaws have been identified, reported, fixed, and the fix has been validated.
Remediation and Final Testing: Tools of the Trade
A challenge that presents itself for remediation is collaboration and tracking the status of findings. Many different teams or divisions may need to be brought together. Some of the teams will lack context of the vulnerabilities because they were not involved with the testing or read-out portions of the engagement. System or data owners may be unfamiliar with the “how-to’s” of fixing vulnerabilities identified. The system and application owners may need to ask questions, get guidance, and someone has to be tracking all of these things. If no one is tracking the status, then there is no accountability and the effort to remediate the vulnerabilities will fall by the wayside.
To counteract a lack of accountability and progress tracking, typical tools employed are related to project management. Many organizations employ ticketing or service management solutions like Jira, Zendesk, ServiceNow, or Remedy. Flaws are entered into these systems and their progress is tracked.
Others may use more manual methods, such as using office automation software; Microsoft Excel, Word or Project documents are stored in wiki systems or document management solutions, al la SharePoint or OpenDocMan, and manually updated by individuals.
Retesting tools are normally the automated or manual methods the security service providers originally used to identify the flaw in the first place. Many open source tools are used such as NMAP, Nikto, or other scripts derived from the open source security tool community. Other tools include automated vulnerability scanning solutions.
Benefits and Challenges of the Remediation and Final Testing Phase of Penetration Testing
When it comes to retesting, ensuring a documented repeatable process is followed is very important. If the retest is not an “apples to apples” comparison, and the same methodology, technical tooling, and identification method is not used, the results may be inaccurate. From the perspective of the team performing the technical retesting activity it is important that flaws are categorized and identified in the same manner as the original test. This can become problematic when different individuals are retesting, when they did not perform the original test. The largest benefit to retesting is quantitatively proving that observed flaws have been taken care of. This will give the business or data and system owners assurance that their security posture has been strengthened. But, if the results of the retesting are suspect or confusing, the genuine security posture of the organization may be a mystery or poorly communicated.
Communication, collaboration, accountability, and oversight make these closely related phases work in concert. Ensuring there is someone owning the process(es) is important. Also, ensuring that a system is used that not only tracks the status of flaws but can also enable collaboration and communication is a huge benefit; however, if it’s not done (or done well) the system can be a detriment to effective remediation and retesting. What tends to happen is the owner of the flaws, or the owner of remediating the results, is overwhelmed by events, is not empowered to accurately track the flaws nor provide answers to the questions that app and system owners have regarding how to remediate. This situation can end up causing chaos and prolonging the remediation process. In worst case scenarios, remediation simply doesn’t happen, and the value of testing is lost.
Use PlexTrac Every Step of the Way
The PlexTrac platform has built-in vulnerability status tracking and reporting and also integrates with Jira and Service now. The ability to assign findings and assets to owners can also drive accountability. The remediation and final testing workflows are a part of PlexTrac’s core DNA.
PlexTrac saves pentest teams time and resources while also ensuring that organizations receive the maximum value out of their offensive assessments and testing, whether outsourcing or conducting them internally.