Penetration Testing
- TL;DR on Penetration Testing:
- What Is Penetration Testing?
- Why Is Penetration Testing Important?
- What Are Common Types of Penetration Testing?
- What is the Penetration Testing Process?
- Real-World Examples of Pentesting:
- What Are the Differences Between Pen Testing vs. Vulnerability Assessments?
- Penetration Testing Tools & Certifications
- What Is Dynamic Cone Penetration Testing?
- How to Learn Penetration Testing?
- How Can PlexTrac Help With Penetration Testing?
- FAQs About Pentesting
- Related Resources
TL;DR on Penetration Testing:
You don’t always have time to read all the little details. So we put together a quick summary of what you need to know about penetration testing for you.
Penetration testing in cybersecurity is a proactive, offensive security practice that simulates realistic cyberattacks to identify and exploit vulnerabilities within IT infrastructure. It is a form of ethical hacking used to identify security gaps such as unauthorized system access, out-of-date software, misconfigured servers, or weak passwords.
Penetration testing reduces security risks faster, helps organizations meet regulatory compliance (like HIPAA, SOC 2, PCI DSS), enables proactive threat detection, and strengthens security posture by remediating potential security exploits for organizations of all sizes.
The pentest process typically includes these steps:
- Setup & Planning: Define goals, scope, and testing rules of engagement.
- Discovery & Enumeration: Gather intelligence on the target and set goals.
- Detection & Exploitation: Attempt to exploit vulnerabilities and remain undetected.
- Post-Exploitation, Reporting, & Read Out: Create an actionable report with remediation recommendations.
- Remediation & Final Testing: Repair security flaws and retest to ensure resilience.
What Is Penetration Testing?
Penetration testing, also known as pen testing or pentesting, is a proactive offensive security practice that simulates realistic cyberattacks to identify and exploit vulnerabilities across systems, networks, or applications. Once weaknesses are identified, pentesters provide recommendations for remediation.
The NIST definition of penetration testing is a “test where pentesters target individual binary components or the application as a whole to determine whether intra or intercomponent vulnerabilities can be exploited to compromise the application, its data, or its environment resources.”
Simply speaking, a pentester is an ethical hacker who attempts to infiltrate systems just as a real threat actor would. However, they are typically “hacking for good” to prevent real attacks by identifying security gaps, such as unpatched software, outdated systems, misconfigured servers, or weak passwords.
Unlike vulnerability scanning, which relies primarily on automated tools to merely identify weaknesses, a pentest may use manual pentesting or automated pentesting. Either way, accurate intrusion testing requires expert-level pentesters who utilize security flaws to their advantage and sneakily slip through the cracks to escalate privilege with the ultimate goal of helping the organization strengthen its defenses.
Some penetration testing examples include:
- Cloud penetration testing: A pentester can potentially hack into storage buckets and virtual machines. Then, they can escalate privilege to access more critical assets within the cloud infrastructure.
- Black box testing: A penetration test service provider may run a pentest without prior knowledge of the systems, like they do with black box testing. Still, they gather their own intel and simulate attacks to pinpoint vulnerabilities.
- Physical penetration testing: A tester, for example, could sneak through a passkey door after an employee walked through and snag an unlocked laptop.
Watch this video to get the inside scoop on pentesting: Hack Your Pentesting Routine: Secrets for Success.
Why Is Penetration Testing Important?
Imagine if you could stop a small leak before a basement floods. You can think of penetration testing in a similar way. Penetration testing supports cybersecurity efforts by identifying security weaknesses before malicious actors can exploit them. If you find potential risks before exploitation, you can save an average of $10.22 million, according to a recent IBM report.
The primary purpose of penetration testing is to ensure your security controls are effective, while helping you reveal security gaps and confirm you’re meeting compliance requirements.
Running a pentest is great, but pentesting frequency matters. A once-a-year pentest is no longer considered sufficient, especially with the new compliance regulations, like DORA. Continuous pentesting is quickly becoming more essential, but also more doable for teams of all sizes.
Regular penetration testing can help your business identify weaknesses. Pentesters should provide a thorough report of their methods, findings, and remediation suggestions. From there, the evaluated business should take action to reduce security risks, meet regulatory compliance (HIPAA, SOC 2, PCI DSS), and take a more proactive approach to threat detection.
Simple Penetration Testing Use Cases:
- Small to Medium-Sized Businesses (SMBs): SMBs and startups can leverage penetration testing companies to gain greater visibility into exploitable security gaps without bringing in an in-house security team.
- Enterprises: Large enterprises and Fortune 500 companies can utilize pentest services to meet compliance, secure complex infrastructures, and test zero-trust implementations.
Government Agencies: Public entities can utilize a penetration test service to prove security reliability and maintain trust of critical systems and citizens’ personally identifiable information (PII).
What Are Common Types of Penetration Testing?
Penetration testing services and reports can comes in various forms depending on the target and method of attack. Here are a few common penetration testing types:
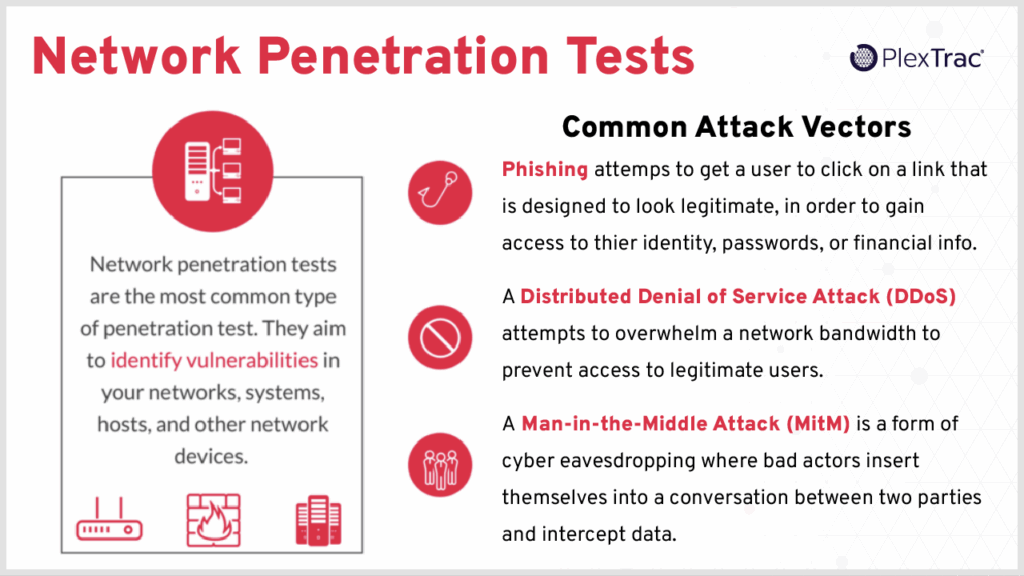
Network Pentests
Network penetration testing focuses on internal and external penetration testing to determine the level of security on each network. Internal testing is run within the organization’s network, while external testing is done from an external network, simulating a real-world attack.
Network pentests are the most common pentest. It analyzes the security within firewalls, routers, servers, and switches.
Physical Pentests
Although it’s less often exploited these days, physical penetration tests assess physical security controls, like door locks, badge systems, ID checks for restricted access areas, and other potential entry points into a facility.
Physical pentests mimic malicious actors by attempting to breach security gateways through social engineering, lock-picking, and bypassing access controls and surveillance. If even one attack vector is successful, an attacker could take control of your business and its data. So even if physical breaches aren’t as common as Jurassic Park may make them seem, they are important to test.
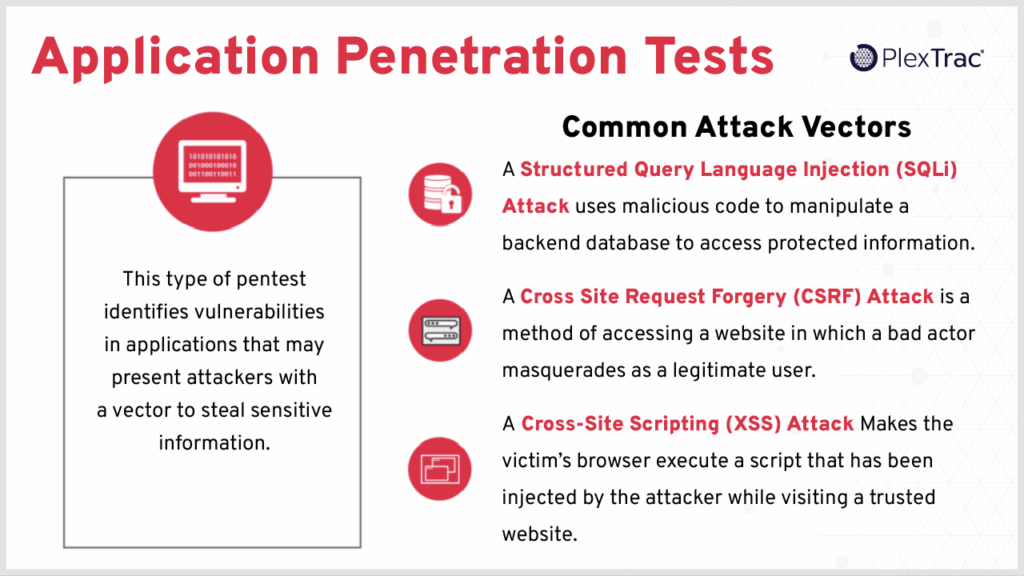
Software, API, and Application Penetration Testing
Application pentesting and software penetration testing, as you may have guessed, target software, web applications, and application programming interfaces (APIs) to uncover issues, such as SQL injection or broken authentication.
Penetration testing in software testing is performed across web applications to identify vulnerabilities in the application’s code, such as cross-site scripting.
Wireless Penetration Testing
Wireless penetration testing, aka Wi-Fi penetration testing, simulates cyberattacks on wireless networks to find vulnerabilities in the network’s security protocols, encryption, or access controls.
Business wireless networks require testing to ensure cyberattackers won’t log into the business Wi-Fi and gain unauthorized access to data. In addition, pentesters will assess the network for security gaps, like lax encryption, device monitoring, wireless network structure, and weak passwords.
Social Engineering Pentests
Social engineering (SE) tests often include phishing, pretexting, or baiting attacks to evaluate employee susceptibility. SE assessments leverage real-world attack scenarios and TTPs (tactics, techniques, and procedures) to raise employee awareness and uncover less-than-ideal security policies and technical controls that should be able to detect SE attacks automatically.
According to a recent PurpleSec report, 98% of cyberattacks leverage social engineering, where threat actors deceive users into revealing security intel, such as logins or passwords. Pentesters often use TTPs such as phishing, vishing (voice-based scamming), and smishing (text-based scamming) to scrutinize and enhance employee training and safeguards.
IOT/Mobile Penetration Testing
IOT/Mobile penetration testing helps identify vulnerability exploits on mobile devices as well as all devices connected to that network, which could lead to vulnerable vectors for an attacker to exploit. This type of pentest pinpoints hardware or software security gaps in connected devices that are not covered within standard network penetration tests. These tests may also include any products your company sells, as well as mobile application penetration testing.
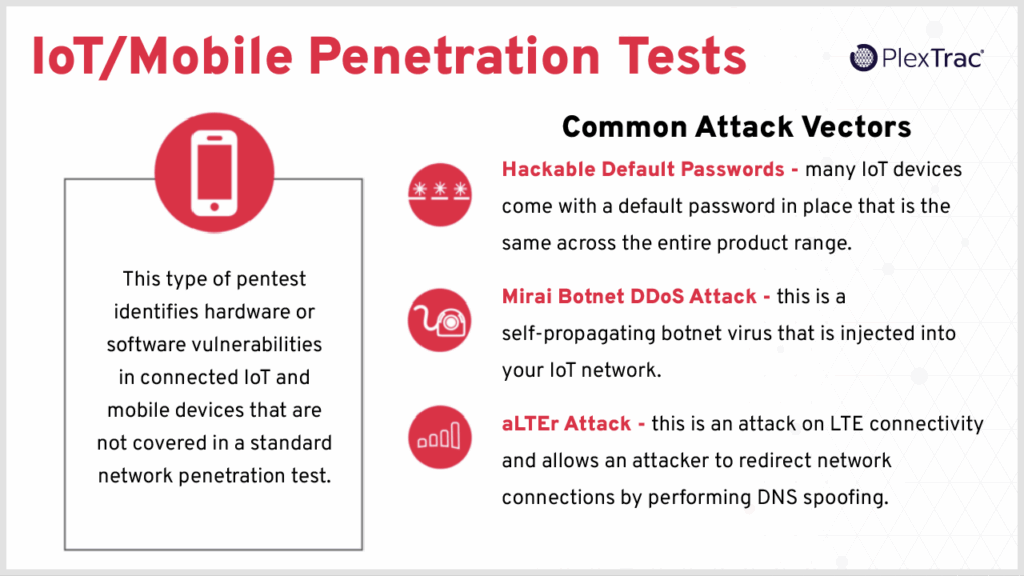
Common weaknesses in devices on your Internet of Things (IOT) network include unencrypted data, even at rest, or use of insecure protocols, like transferring unencrypted data.
As mentioned, IOT includes the interconnected network of physical devices, but it may also refer to smart devices within vehicles, buildings, and other items embedded with sensors. Ensuring they are safely controlled and monitored, even remotely, is important for your organization’s security.
Cloud Penetration Testing
Cloud penetration testing assesses cloud infrastructure configurations, such as identity and access management (IAM), and deploys applications to unveil issues around any cloud complexity misconfigurations, or abused API keys, microservices, or user accounts.
Container Penetration Testing
Container penetration testing examines and tests containers for container image security and the underlying host system. Although container security flaws may appear similar to those in applications, such as unauthorized systems or data access, the container image itself could introduce breakout vulnerabilities that may grant access to the host system. Container testing may also leverage image scanning, runtime security testing, and host and guest network pentesting.
PCI Penetration Testing
PCI penetration testing, also known as Payment Card Industry data security standards (PCI DSS) testing, specifically focuses on evaluating an organization’s cardholder data environment (CDE) security and ensuring compliance with the PCI DSS requirements. Running proactive pentests on PCI systems helps prevent breaches and protects sensitive cardholder information, all while meeting the required compliance.
What is the Penetration Testing Process?
The penetration testing methodology includes several steps that vary slightly across different organizations, but they always have these phases in common: planning, discovery, exploitation, reporting, and remediation.
Below, we’ll walk through a quick summary of each penetration phase.
1. Setup & Planning
The setup and planning of a pentest may be one of the most important steps in the penetration testing process. Prepping for the pentest with proper project management that notes every part of the pentest, such as the people involved, processes, scope, goals, and testing rules of engagement, is essential to success.
Questions to ask in this phase include:
- Why are we here?
- Who is on the team?
- What systems are tests to be run on?
- What is the success criterion?
- What is the required deliverable?
Side note: The PlexTrac platform provides the perfect, secure place to organize all this information for better communication and collaboration both internally with blue and red teams, and externally with clients of all sizes and needs.
2. Discovery & Enumeration
In the Discovery & Enumeration Phase, testers validate assumptions made in the first phase by collecting information about the organization’s IT infrastructure and identifying potential vulnerabilities that an attacker could exploit.
Discovery tools to leverage may include:
3. Detection & Exploitation
For most pentesters, the Detection and Exploitation Phase is where the true fun begins. In this step, they’ll work on gaining access by exploiting discovered vulnerabilities and determine if persistent access can be maintained without detection.
Important note: Be sure to review rules of engagement (RoE) for any constraints before hacking your way through systems. This ensures smooth operations and keeps you on task.
4. Post Exploitation, Reporting, & Read Out
The Post-Exploitation, especially the Reporting and Read-Out phases, may seem tedious and daunting, but they are critical to security and penetration testing. In this phase, the tester prepares a clear, actionable report that summarizes the findings and recommendations for remediation.
Feeling drained from all the reporting? Maximize your pentest reporting efficiency with these 5 tips for writing better cybersecurity reports.
5. Remediation and Final Testing
So you delivered your report, now what? The next phase in the penetration testing process is Remediation and Final Testing. Remediation is the primary purpose of a pentest. Sure, identifying vulnerabilities is important, but without mitigating the risk, there is no true added value.
In this phase, you’ll want to help the organization show progress, meet compliance requirements, and retest the remediations to ensure improvement in the overall security posture.
Additional Penetration Testing Stages
Looking for a more in-depth pentesting methodology? Check out our Introduction to All the Phases of Penetration Testing with the full 10-step process.

P.S. If you’re interested in shortening your penetration testing cycle, be sure to read the Hack Your Penetration Test Routine Whitepaper for the best tips and tricks.
Real-World Examples of Pentesting:
Now that you get the concept of penetration testing, it’s time to apply it to the real world. Here are a few penetration testing examples.
Penetration Testing Example 1: Spinning Webs of Malicious Code
In order to find security gaps within an application, a pentest injects malicious code for cross-site scripting into a website and attempts to overload it with traffic for a denial-of-service attack. Once they discover how systems react and find any security gaps, they note the methods used along with the found vulnerabilities. Within the report, they should also provide prioritized remediation recommendations.
Penetration Testing Example 2: Failing Health Systems With Simulations
A penetration test service provider was called in to assess a reputable hospital to test systems to see if it’s possible to infiltrate personal identifiable information (PII). In this pentest use case, the pentester was able to use a brute-force attack through password spraying to access an employee’s logins and then continued to laterally move through systems to escalate privilege and access the patient records.
Once the pentester has finished the set mission, they create a detailed report outlining each tactic, escalation, and suggested remediation recommendations to prevent a potential breach. In this case, of course, they would recommend better security protocols around strong password requirements, as well as other vital tidbits.
What Are the Differences Between Pen Testing vs. Vulnerability Assessments?
Although commonly confused, pentests are not the same as vulnerability scans. Penetration testing and vulnerability scanning are critical components of cybersecurity that aim to identify vulnerabilities. However, they differ in their approach and objective.
What Is Pentesting?
Penetration testing is the process of simulating an attack on a system, network, or application to identify and exploit vulnerabilities before a real malicious actor could leverage them for unauthorized access, cause damage, or use them for financial gain.
What Is Vulnerability Scanning?
Vulnerability scanning is the process of identifying and analyzing vulnerabilities in computer systems, networks, applications, and databases. In other words, it’s a thorough scan to find existing security gaps.
How Do Pentesting and Vulnerability Assessments Differ?
While vulnerability assessments are useful and should be run regularly to identify correctable weaknesses, penetration testing goes far deeper with experts who actively exploit the security weaknesses they find. As it sounds, pentesters penetrate deeper to see just how much damage they could do from their initial entry point. Penetration tests also evaluate the physical facilities and human side of an organization through phishing schemes and other methods to find access points.
Here’s a quick overview of vulnerability assessments vs pentesting.
Table: The Differences Between Vulnerability Assessment vs Penetration Testing
| Feature | Vulnerability Assessment | Penetration Testing |
| Objective | Identify known vulnerabilities | Find and exploit vulnerabilities |
| Tools | Automated scanners | Automated and manual tools as well as manual testing |
| Depth | Surface-level scans | Greater depth with research and simulated attacks |
| Output | Document of found issues | Detailed report of exploited paths, risk context, and remediation suggestions |
| Frequency | Regularly, often monthly | Sometimes only once or twice a year, but weekly is highly recommended for optimal security posture. |
Do Pentesting and Vulnerability Scanning Work Together?
Yes, using vulnerability scanning and pentesting together provides organizations with a more comprehensive understanding of their cybersecurity posture. Pentesting gives a realistic picture of how their infrastructure would stand against real-world attacks and helps identify security gaps that a vulnerability scan may miss. Together, though, they can help spot vulnerabilities quickly, provide prioritized remediation recommendations, and fortify the organization.
Discover how you can empower your workflows with AI and leverage pentest reporting together with vulnerability management in our blog.
Penetration Testing Tools & Certifications
Popular Penetration Testing Tools
There is a wide range of security and penetration testing tools based on the specific stage of testing and the areas tested. A few of the most popular pentest tool categories include the following.
Reconnaissance Tools
Reconnaissance tools gather information about a target. These recon tools may be based on the network, application, or used to gather open source intelligence (OSINT) data — like Shodan and Censys — about an asset, application, network, or organization. Some examples of reconnaissance tools are port scanners, network and application service banner grabbing, and DNS information gatherers. Reconnaissance tools include: Nmap, Recon-ng, Maltego, Fierce, Shodan, Censys, and theHarvester.
Vulnerability Scanners
Vulnerability scanning tools probe and respond to identify known vulnerabilities within information systems. These scanners check conditional logic to determine if a vulnerability exists by examining the response generated from the target. Vulnerability scanners include: Nessus, OpenVAS, Nikto, and Skipfish.
Proxy Tools
Proxy tools act as a “middleman” per se for the network and application traffic inspection. Network proxy tools are used to mask, hide, or change the original source of TCP/IP-based traffic. Proxy tools also provide the ability to view and interact with data that would typically be hidden from a user interface perspective. Proxy tools include: Burp Suite, OWASP ZAP, and Fiddler.
Exploitation Frameworks
Exploitation frameworks and systems initiate access operations and take advantage of vulnerabilities. These tools can be highly specialized in command and control (C2) frameworks or may be utilized as staging platforms to create and customize exploits contained within the framework. Exploitation framework tools include: Metasploit, Armitage, and Exploit Pack.
Post-Exploitation Tools
Often, exploitation frameworks contain built-in post-exploitation capabilities. Some of the most common post-exploitation tools are community-built scripts or single-use applications that establish persistence, gather information, or aid in escalating privilege. Post-exploration tools include: Metasploit Framework, Mimikatz, and C2 Frameworks like Covenant and PoshC2.
Web Application Testing Tools
Web application testing tools exploit vulnerabilities across web applications to prevent cross-site scripting (XSS), authentication bypass, insecure configurations, or SQL injection attacks. Web application testing Tools include: BurpSuite, Open Worldwide Application Security Project (OWASP) Zed Attack Proxy (ZAP), SQLMap, DirBuster, and Wapiti.
Wireless Testing Tools
Wireless testing tools evaluate the wireless network to pinpoint misconfigurations, weak encryption, unauthorized access points, or security gaps to prevent infiltration. These tools help identify weak or broken Wi-Fi encryption, including WEP, WPA, and WPA2 flaws. Wireless network testing tools include: Aircrack-ng, Kismet, Wifite2, Fern, and Reaver.
Social Engineering Tools
Social engineering (SE) tools assess human susceptibility to social engineering attacks. Using simulated attacks like phishing, baiting, pretexting, and physical infiltration, SE tools help raise security awareness and test detection automation. SE tools include: Social-Engineer Toolkit (SET), Browser Exploitation Framework (BeEF), and Medusa
Password Cracking Tools and Brute Force Tools
Password cracking tools analyze password strength by attempting to break in through weak or regularly reused passwords. Leveraging these tools during pentests helps discover poor password policies and bad password storage practices. Password cracking and brute force tools include: Hydra and John the Ripper.
Reporting, Collaboration, and Management Tools
Reporting, collaboration, and management tools make sense of cumbersome and messy data outputs and present the findings easily to both technical and non-technical folks for clear communication and easy collaboration.
PlexTrac embodies all three of these tools as users are able to efficiently gather the required data, triage, and work with findings directly in the platform, and generate meaningful reports with actionable insights that are easy to create and read.
All-In-One Suite Tools
There are also all-in tool suite operating systems that you can choose from depending on the organization’s niche, needs, and workflows. Some of these all-in-one tools include: Kali Linux, Parrot Security OS, BackBox, BlackArch, Pentoo, DEFT (Digital Evidence & Forensics Toolkit), Tails, Ubuntu Security Remix, ArchStrike, Cyborg Hawk.
Discover the most popular penetration testing tools in our blog, 30 Products to Support Your Pentesting Efforts This Year.
Helpful Pentesting Certifications
There’s a plethora of cybersecurity certifications out there to . However, not all of them are exactly what you need. Most certifications will benefit you in some way, but in our opinion, here are some of the best and most popular cybersecurity certifications:
- EC-Council’s Certified Ethical Hacker (CEH)
- ISC2’s Certified Information System Security Professional (CISSP)
- CompTIA’s Security+, Pentest+, Cybersecurity Analyst (CySA+)
- ISACA’s Certified Information Security Manager (CISM)
- NIST Cybersecurity Framework (NCSF)
- CompTIA’s Advanced Security Practitioner (CASP+)
- ISACA’s Certified Information Systems Auditor (CISA)
- ISC2’s Certified Cloud Security Professional (CCSP)
- EC-Council’s Computer Hacking Forensic Investigator (CHFI)
- Cisco Certified Network Associate (CCNA) Security
- eLearnSecurity Junior Penetration Tester
Additional certifications to consider for your career advancement include:
- OffSec Offensive Security Certified Professional (OSCP+)
- GIAC Penetration Tester (GPEN)
- Practical Network Penetration Tester (PNPT)
While these are known as some of the best cybersecurity certificates out there, not all of them are made for everyone. Be sure to do your research and choose what fits best for you and your ideal career path.
Are cybersecurity certifications worth the investment? Learn more by checking out our Certification Crash Course blog.
What Is Dynamic Cone Penetration Testing?
A dynamic cone penetration (DCP) test is a geotechnical method used to measure soil strength and stiffness for construction purposes. Although it may sound like a cybersecurity term, it’s unrelated.
If you want to think of them as similar in a way, they both penetrate things. A DCP test involves driving a cone into the ground to penetrate and measure its resistance. Cybersecurity penetration testing works to penetrate what you can’t see on the surface of an organization’s infrastructure by simulating attacks on computer systems to find and remediate vulnerabilities.
How to Learn Penetration Testing?
Becoming a penetration tester is not an easy task. It requires a unique set of skills, including technical expertise, creativity, problem-solving, and communication skills. Additionally, the job is highly demanding and involves a lot of pressure and tight deadlines.
1. Start with Technical Education
Having a technical education in computer science, IT, information architecture, cybersecurity, and any other tech background is usually helpful for becoming a penetration tester. This type of education could be acquired from colleges, free online resources like YouTube, bootcamps, or technical programs. Some even recommend TryHackMe, SANS Pentesting Courses, Cybrary, INE, OffSec FreePen-200, or Hack The Box. Building a foundation for pentesting concepts that involve the use and abuse of technology can be very beneficial for new pentesters.
Pro tip: There are many courses outside of pentesting you can take to increase your field knowledge, such as training in networking, wireless, or cloud security. Or change course for other relevant learning on reverse engineering, cryptography, and social engineering.
2. Get Hands-On Training
Of course, there’s nothing better than real-world experience and getting your hands on the keyboard at internships or full-time jobs in cybersecurity. They can provide valuable experience for aspiring penetration testers, even if it’s not directly in pentesting, such as IT support or a system admin.
3. Obtain Relevant Certifications
There are tons of that can expand your knowledge, skills, and experience. These certs show potential employers and clients that you’re not only dedicated to your practice but that you have the training to know what to do. Combining certifications with hands-on experience proves to employers you’re a well-rounded cybersecurity expert.
4. Get Real World Experience
Of course, there’s nothing better than real-world experience, like Internships or full-time jobs in cybersecurity. They can provide valuable experience for aspiring penetration testers, even if it’s not directly in pentesting, such as IT support or a system admin.
5. Keep Up to Date with the Latest in Pentesting
Stay up-to-date with the latest trends, techniques, and tactics. Many recommend some light reading on SANS Institute, Dark Reading, Krebs on Security, OWASP, Hack The Box, and SecurityTube to be in the know.
Don’t forget to join communities like Reddit’s r/netsec or Discord groups to learn from your peers. Plus, it never hurts to crack open a good book.
Want to learn more penetration testing tips and discover what qualities employers hunt for? Check out the Top 6 Qualifications Employers in Cybersecurity Look For.
How Can PlexTrac Help With Penetration Testing?
PlexTrac’s AI-powered platform was made for pentest reporting and threat exposure management. You can efficiently address the most critical threats and vulnerabilities while getting the most out of your pentesting and exposure management toolsets. Maximize the value and relevance of data from solutions such as PTaaS, BAS, vulnerability management, and attack surface management by aggregating all data within a single space.
PlexTrac is the go-to platform for automating security reporting, aggregating pentest and vulnerability data from various tools and scanners, and effectively prioritizing risk. Request your demo today to learn more.
FAQs About Pentesting
What Are the Types of Penetration Testing?
There are many different targets and attack vectors involved in penetration testing, including:
- Network Pentests
- Physical Pentests
- Software, API, and Application Penetration Testing
- Wireless Penetration Testing
- Social Engineering Pentests
- IoT/Mobile Penetration Testing
- Cloud Penetration Testing
- Container Penetration Testing
- PCI Penetration Testing
Network penetration testing is typically the most common type of penetration test.
What Is the Difference Between a Pen Test and a Vulnerability Scan?
A pen test is a simulated attack on a system, network, or application to identify and exploit vulnerabilities before a real malicious threat actor could. On the other hand, a vulnerability scan identifies known, existing security issues.
What Tools Do Pen Testers Use?
Common penetration testing tools that pen testers use are:
- Reconnaissance tools (Nmap, Recon-ng, Maltego, Fierce, and Kali Linux)
- Vulnerability scanners (Nessus, OpenVAS, Nikto, and Skipfish)
- Proxy tools (Burp Suite, OWASP ZAP, and Fiddler)
- Exploitation framework tools (Metasploit, Armitage, and Exploit Pack)
- Post-exploration tools (Metasploit Framework, Mimikatz, Covenant, and PoshC2)
- Web application testing tools (BurpSuite, Zed Attack Proxy (ZAP), and SQLMap)
- Wireless network testing tools (Aircrack-ng, Kismet, Wifite2, Fern, and Reaver)
- Social engineering (SE) tools (Social-Engineer Toolkit (SET), Browser Exploitation Framework (BeEF), and Medusa)
- Password cracking and brute force tools (Hydra and John the Ripper)
- Reporting, collaboration, and management tools (PlexTrac, Jira, and ServiceNow)
How Often Should Penetration Testing Be Performed?
Probably more than you think. Often, pentests are only run once or twice a year. But that means there are 365 days of potential vulnerabilities that go undetected. Many security experts recommend a pentest frequency of at least once per week, either on a portion of a system or the entire asset. Although that may seem impossible, with the right pentesting tools, it can be easier than you imagine.
With continuous testing, teams can easily spot weak areas and remain alert for the latest Common Vulnerabilities and Exposures (CVEs). In addition, Continuous Threat Exposure Management (CTEM) combined with pentesting helps better manage security gaps, adapt rapidly to growing digital assets and infrastructure, and meet compliance regulations.
Related Resources
How To Become A Penetration Tester
The Most Popular Penetration Testing Tools in 2025: 30 Products to Support Your Pentesting Efforts This Year
Penetration Testing vs. Vulnerability Scanning
Deliver More Value with Innovative Cybersecurity Services
Security Service Providers Defined
PCI Penetration Testing
Reporting and Read-Out Phases: Demonstrate Your Pentest’s Value
Enhance Client Value with Innovative Cybersecurity Services
Hack the 10 Steps of the Pentesting Routine
Remediation and Final Testing Phases: Show Progress, Enhance Security Posture
The Gold Standard of Continuous Pentesting
Pentest Reporting Automation: A Win-Win Proposition for MSSPs
How to Create a Pentest Report in Under 10 Minutes
Manual Pentesting
Video: The Continuous Pentesting Gold Standard: Taking what’s great and making it better
Automated Pentesting
Video: Hack Your Pentesting Routine: Not Another Boring Product Demo
Red Team CybersecurityCommon Vulnerability Scoring System (CVSS Score)