Discovery and Enumeration Penetration Test Phases: A Foundation for Success
Hack Your Pentesting Routine
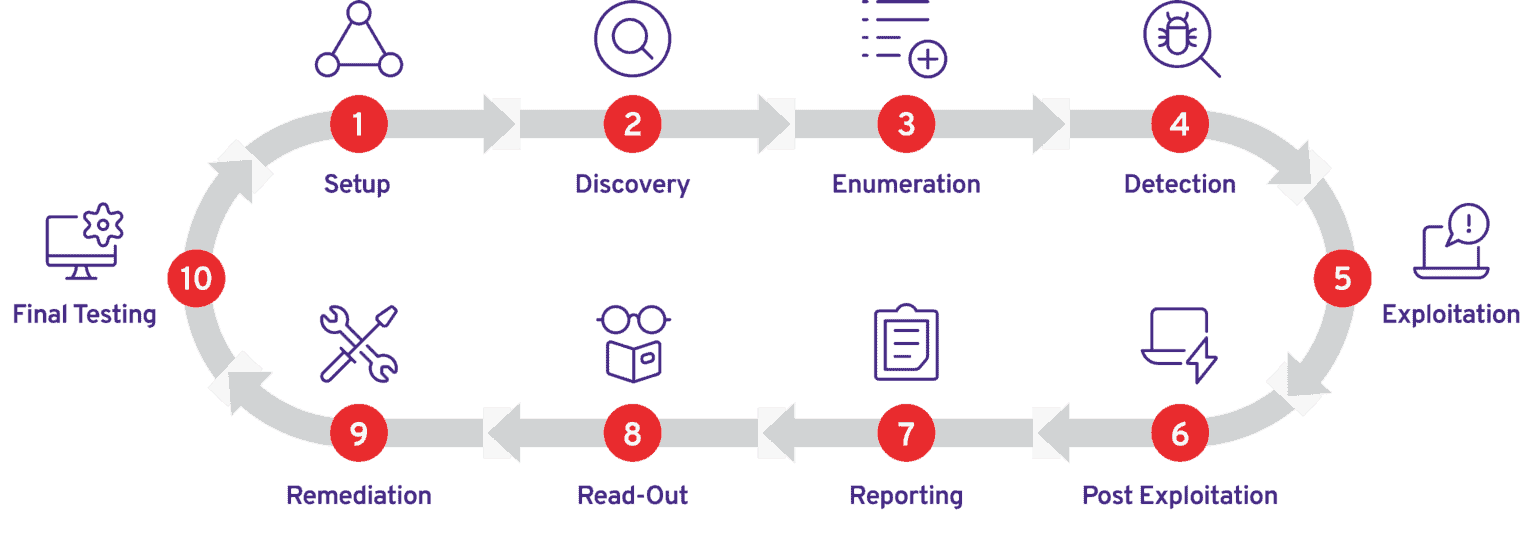
In this Cup O’ Joe series, we’re discussing the ten key phases of a penetration test, talking about the serious pain points in each, and demonstrating how PlexTrac can eliminate these problems.
In my plan, there are 10 phases of the penetration test engagement, each defined by a different group of stakeholders, participants or activities requiring a serious context shift.
Phase One, the Setup Phase, includes every stakeholder in the engagement and provides foundational expectation setting. Why are we here? Who’s on the team? What are we doing? What’s the success criteria we’re using to judge the outcome? What’s the required deliverable? Nail this phase and it’s smooth sailing.
Check out the complete discussion of Phase One in my “Introducing ALL the Phases of Pentesting” article. Want to learn more about how PlexTrac can transform your pentesting practice today? Request a demo.
Penetration Testing Phases Two and Three
Our next phases include
- Discovery
- Enumeration
These phases validate any assumptions made in the Setup Phase and provide a first look into the initial vectors and possible attack chains. Discovery should also be used to validate the scope. Discovery is the asset management phase of an engagement.
I like doing my scope validation in two passes, once before the start of the engagement using third party tools that don’t send a packet at my targets and then again after the start of the engagement. The first round doesn’t require permission and can be performed by any available tester, making scheduling of resources easy.
Discovery and Enumeration: Tools of the Trade
Tools I use in an engagement include the Nmap shodan-api NSE script. It queries the Shodan API for given targets and produces similar output to a -sV nmap scan. I also use Smap, a newer tool that according to its README file “is a replica of Nmap which uses shodan.io’s free API for port scanning. It takes the same command line arguments as Nmap and produces the same output which makes it a drop-in replacement for Nmap.” Both tools produce a file format that can be imported into a number of different tools, including the PlexTrac platform. Smap’s output might have a few false positives as the data it’s querying is up to a week old, but it still provides value.
For DNS discovery and subdomain enumeration I will frequently use a combination of local and online tools. OWASP’s Amass Project is an awesome tool for gathering information from API’s, certificates, DNS, whois, web archives and more. I’ll complement this with Sublist3r for an additional subdomain search using curated lists I’ve compiled over the years.
Urlscan.io is a free service that allows me to review prior scans of a website. urlscan.io will take a screenshot of the page, record the DOM content, JavaScript global variables, cookies created by the page, and output the tech stack it detects. I’ve even used this tool to identify ecommerce sites infected with shopping cart malware
Benefits of the Discovery Phase of Penetration Testing
What I learn in the Discovery Phase could impact the time needed to perform the engagement, so it’s important to take what I’ve learned back to the engagement team and ensure our discoveries won’t require more time, different tooling, or even different skill sets. At least once I’ve identified a mainframe running Apache and DB2 exposed to the Internet and that meant getting another team member to assist in the Exploitation Phase.
Benefits of the Enumeration Phase of Penetration Testing
Enumeration is the step where I begin to look at what I have to work with. It’s where I identify the ports and services, the technology stack, and the people that will be in scope for the engagement. This is the phase where your skills in open source intelligence gathering (OSINT) can really pay off. Tools like Maltego, Recon-ng, and SpiderFoot can capture, aggregate and display vast amounts of information. Here your experience will pay dividends as you sort through and identify what information will take you to the next level.
In the Enumeration Phase, the PlexTrac platform provides secure storage of your evidence and artifacts and lets you create detailed entries on every asset you find — which will set you up for success and time savings later on in the life cycle.
The Best Penetration Testing Begins and Ends with PlexTrac
Make no mistake, PlexTrac lets you re-envision the engagement in ways you’ve never been able to before. Why have senior level operators performing Discovery and OSINT? With all the information at your fingertips, you can easily swap in different testers with different skills at each phase of the engagement, allowing you to execute at the same high level of confidence while maximizing your team.
Read the full Hack Your Pentesting Routine series on the PlexTrac blog.