Blue Teams
Aggregate. Remediate. Communicate.


Vulnerability Management
Aggregate Security Issues from All Sources
PlexTrac is the perfect platform to aggregate security issues and vulnerabilities. Import scanner findings, conduct assessments, and integrate bug bounty tools to create a 360 degree view of your security posture. Visualize your posture in our analytics module to drive faster decision making.
Remediation
Streamline Remediation Efforts
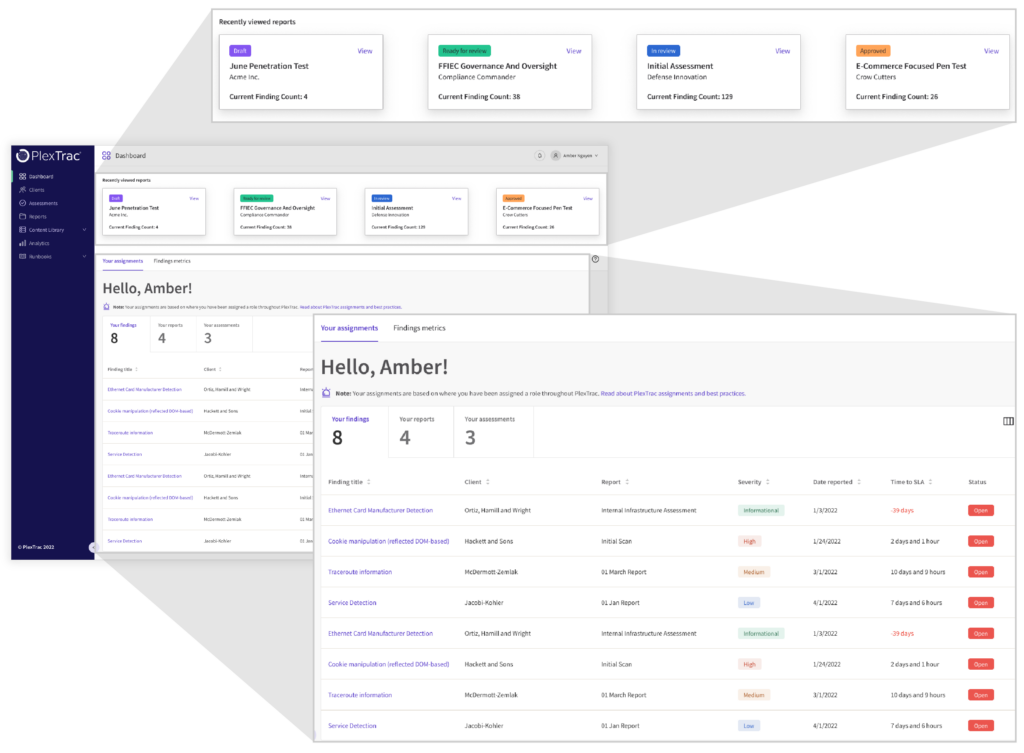
See a snapshot of everything assigned to you upon logging in to the main dashboard via actionable widgets. View, update, and close findings directly from the dashboard view.
Remediation Tracking
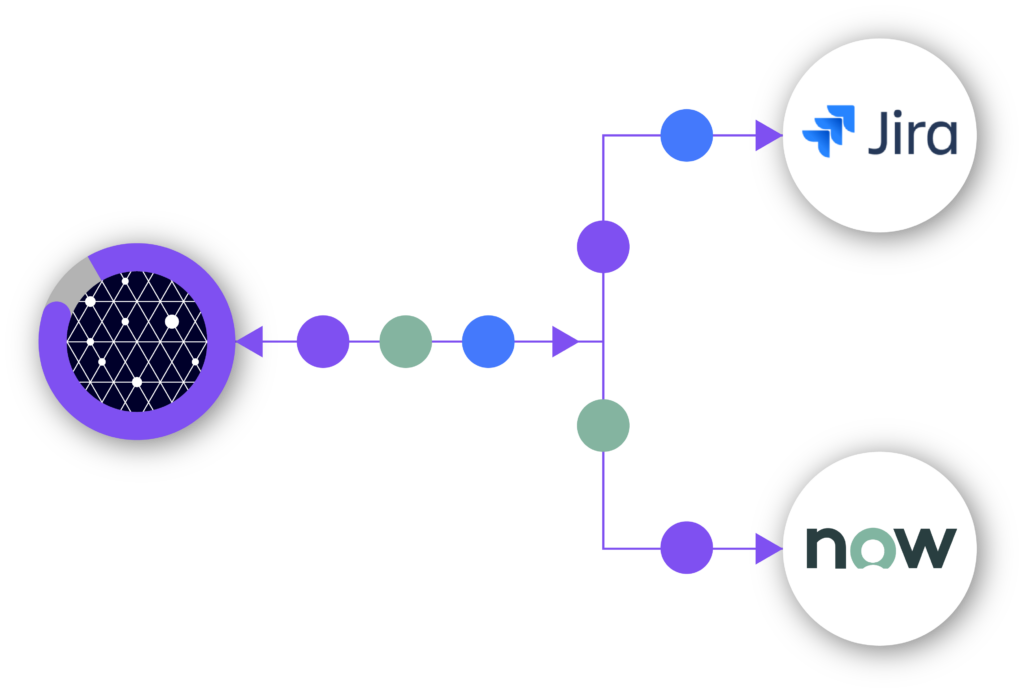
Ticketing Integrations
Our built in integrations with Jira and ServiceNow make it easy for you to continue running existing workflows that are already in place. Coupled with our analytics trends and SLAs, you now gain visibility into your remediation efforts to see how you are trending over time.

Third-Party Risk Management
Understand External Risk
Situational awareness of internal risk is insufficient. It is imperative to also know the risks third-party organizations, including clients and vendors, pose to your organization. PlexTrac was built to aggregate both internal and external security risk, as well as catalyze collaboration on remediation.
Board Reporting
Tell the Story of Your Security Posture
PlexTrac’s reporting and analytics provide a medium through which to communicate the outcomes of investments made in your security program. They support constructive communication by painting a picture that is easy for executives to understand.


