Continuous Threat Exposure Management (CTEM)
Proactively manage exposure risk with PlexTrac for Continuous Threat Exposure Management (CTEM). Consolidate security data from tools and manual testing, automatically prioritize risks based on business impact, and automate remediation and retesting workflows for ongoing, more effective threat management.
Evolve Into CTEM With PlexTrac
Adopt a dynamic and continuous approach to security with PlexTrac for CTEM by consolidating data, prioritizing risks based on business impact, streamlining remediation workflows, reducing risk, and advancing cybersecurity maturity.
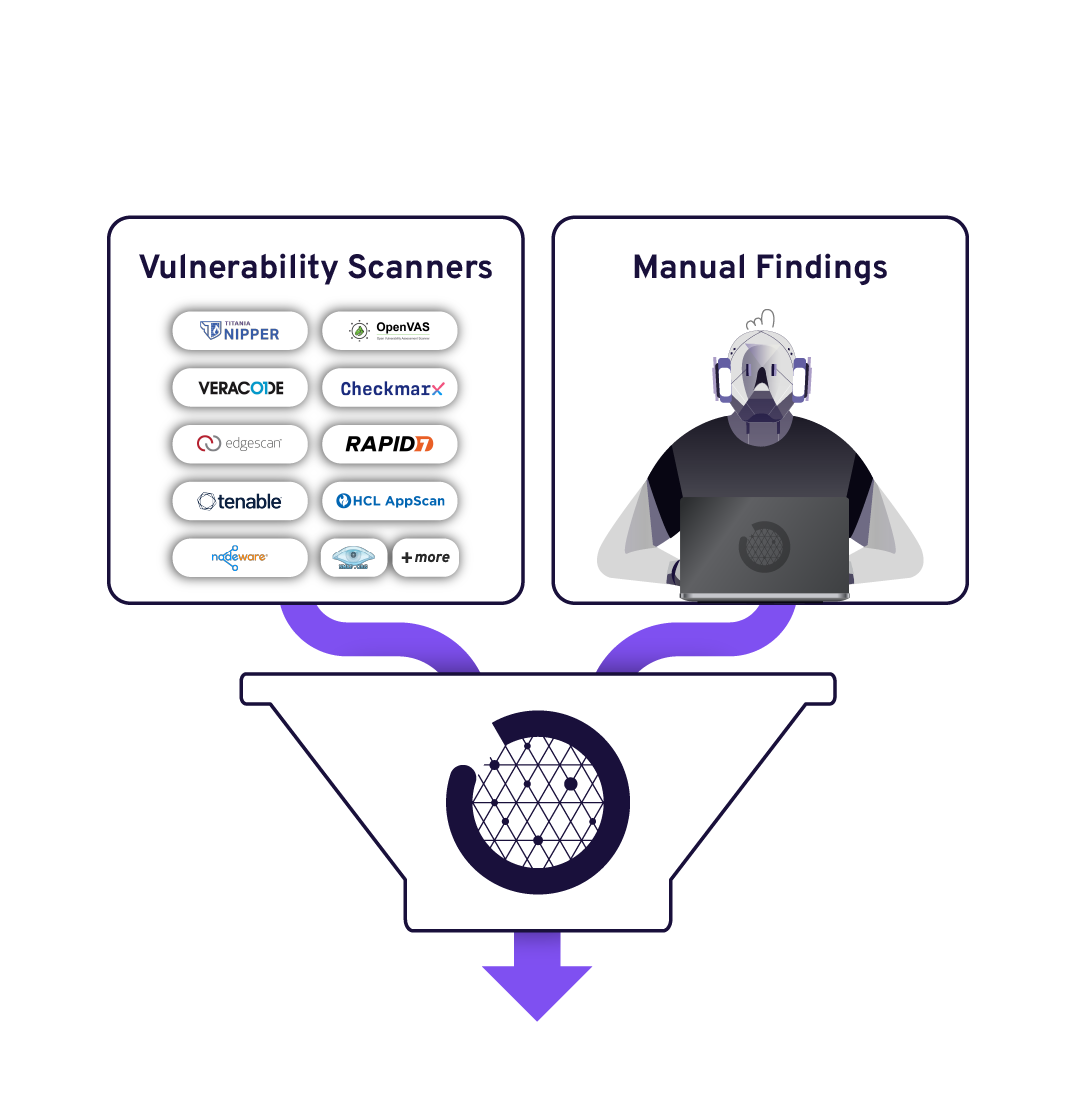
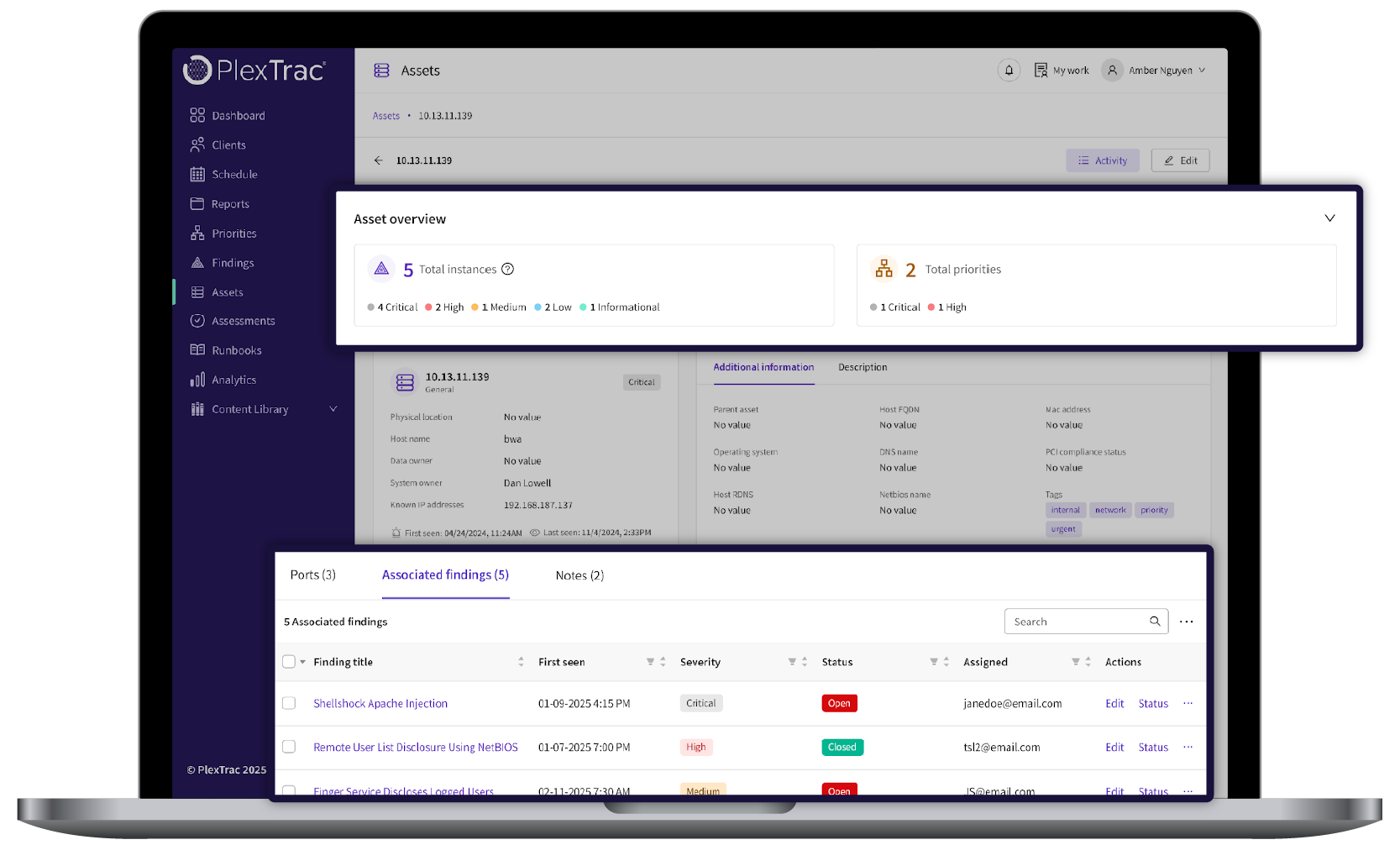
Consolidate all finding and asset data from scanner tools and manual testing into one platform for full attack surface visibility.


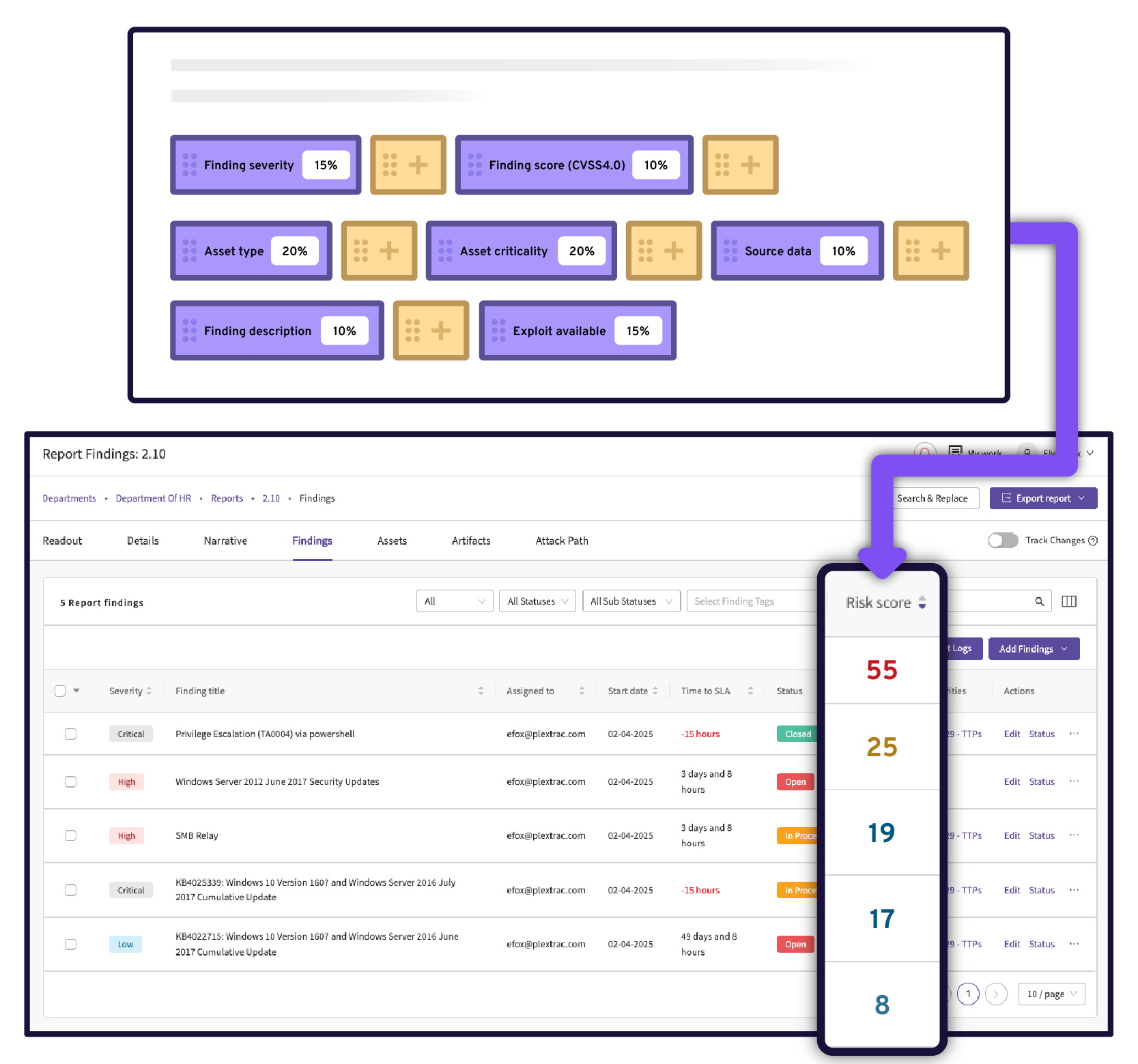
Automatically prioritize individual findings or groups of findings with a risk score based on potential business impact by building fully-configurable risk scoring equations that leverage business context.
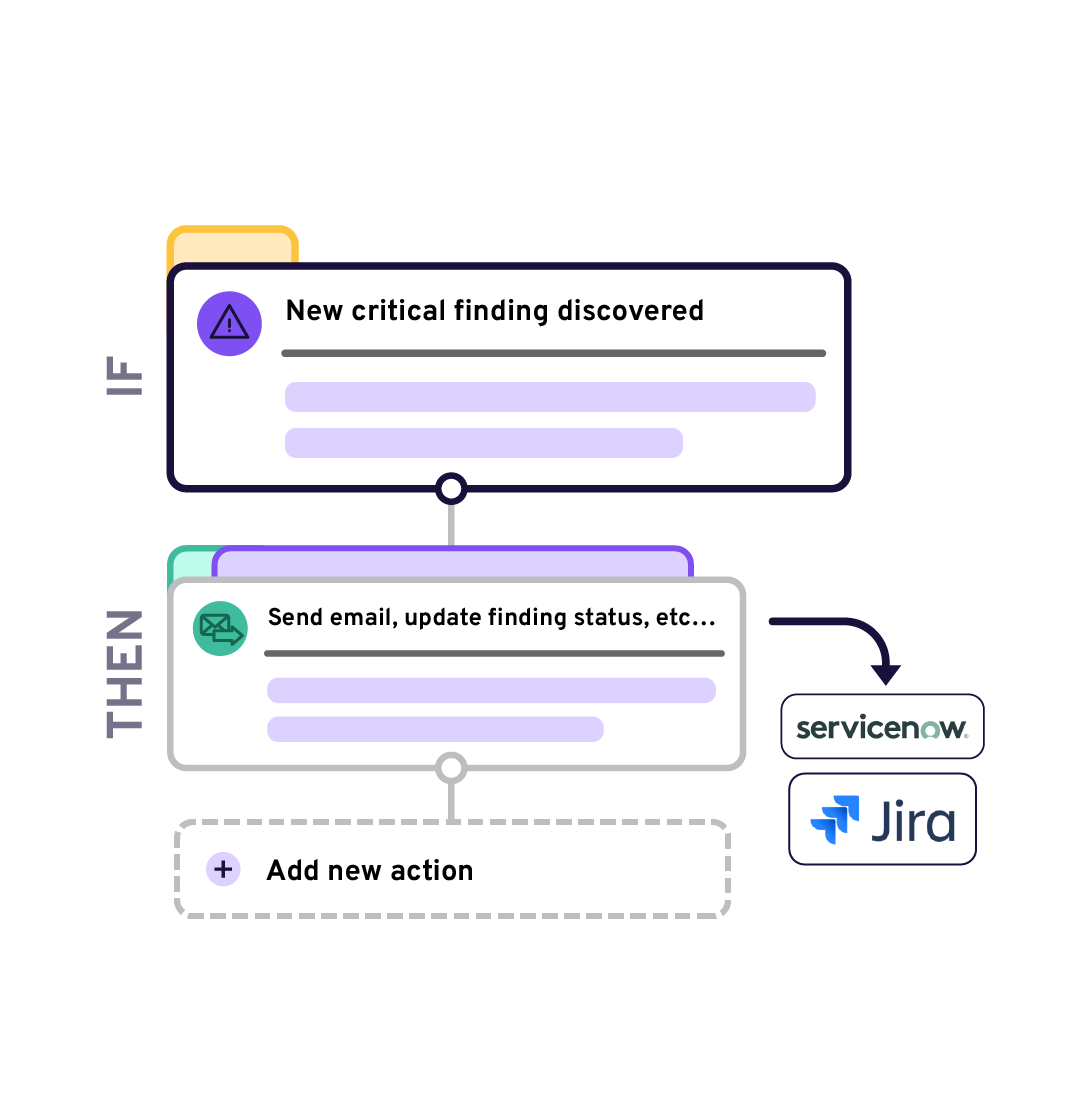
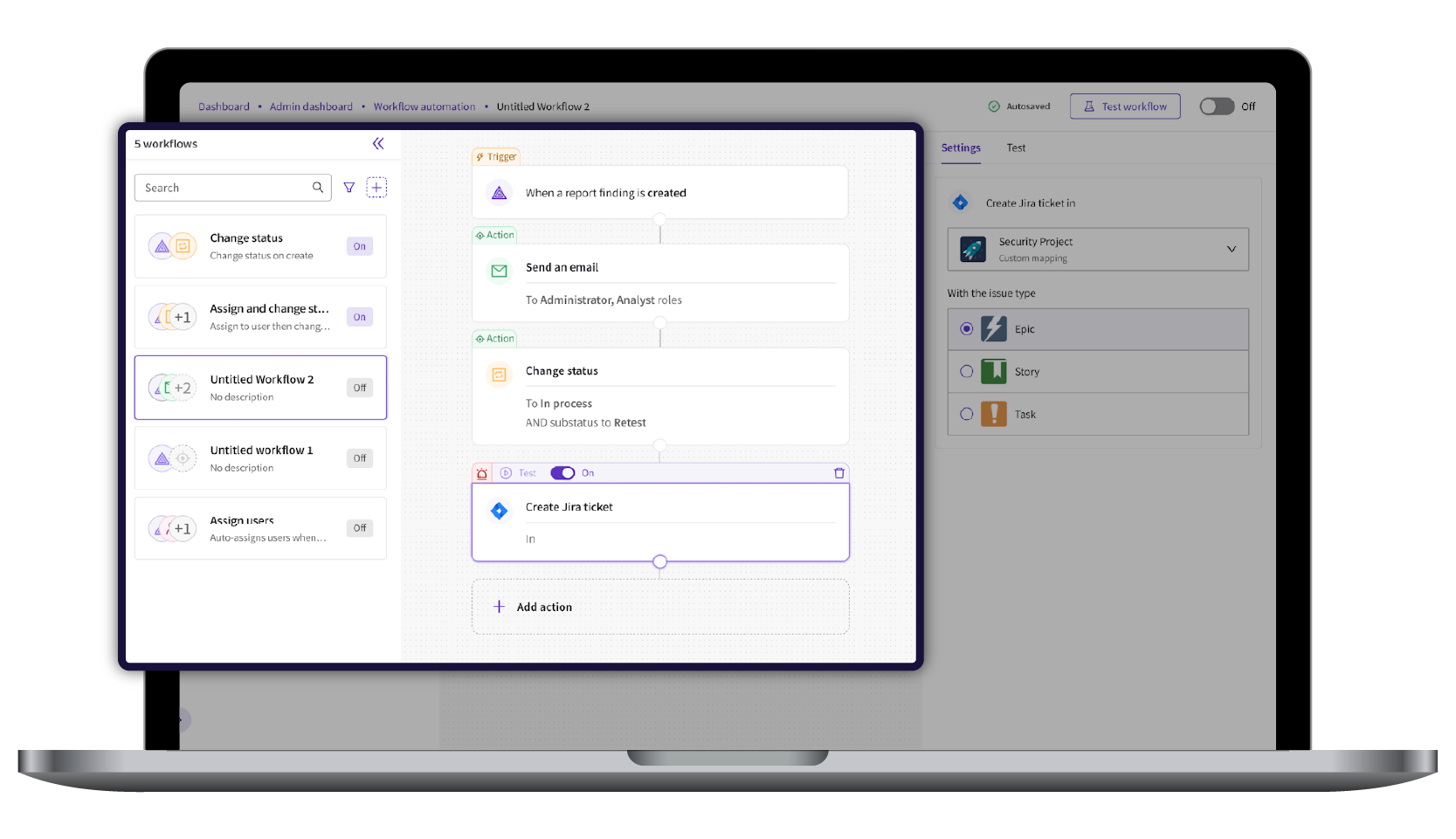
Speed mobilization and eliminate manual tasks with automated remediation workflows. Use trigger events—such as a new critical finding emerging—to automate actions—such as auto-creating a ticket in Jira or sending an email.


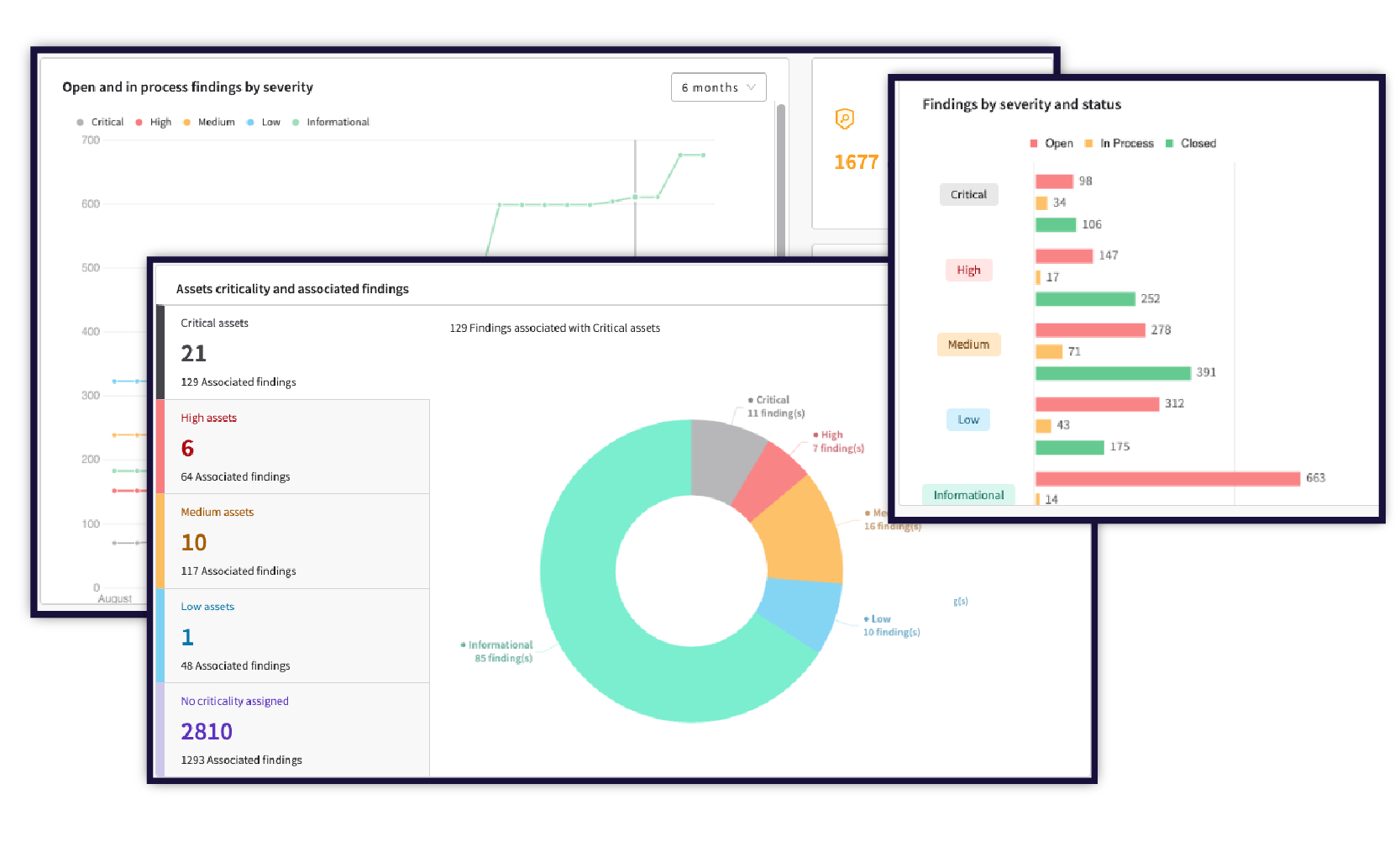
Access real-time insights to make data-driven decisions and communicate risk effectively across your organization. Customize dynamic dashboards for any audience.
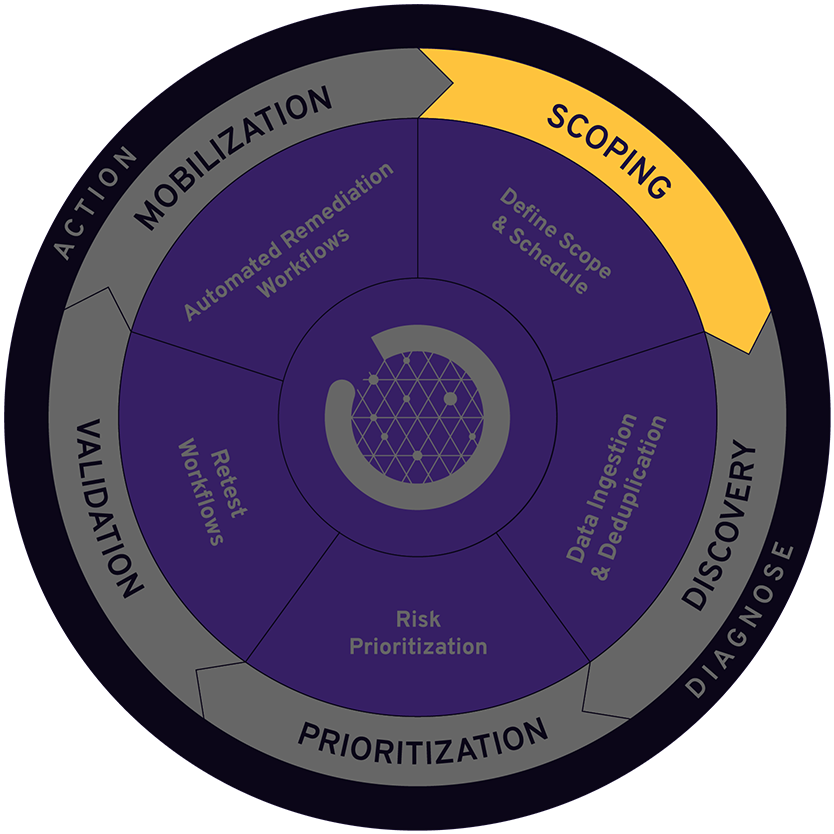
Automate the CTEM Lifecycle With PlexTrac
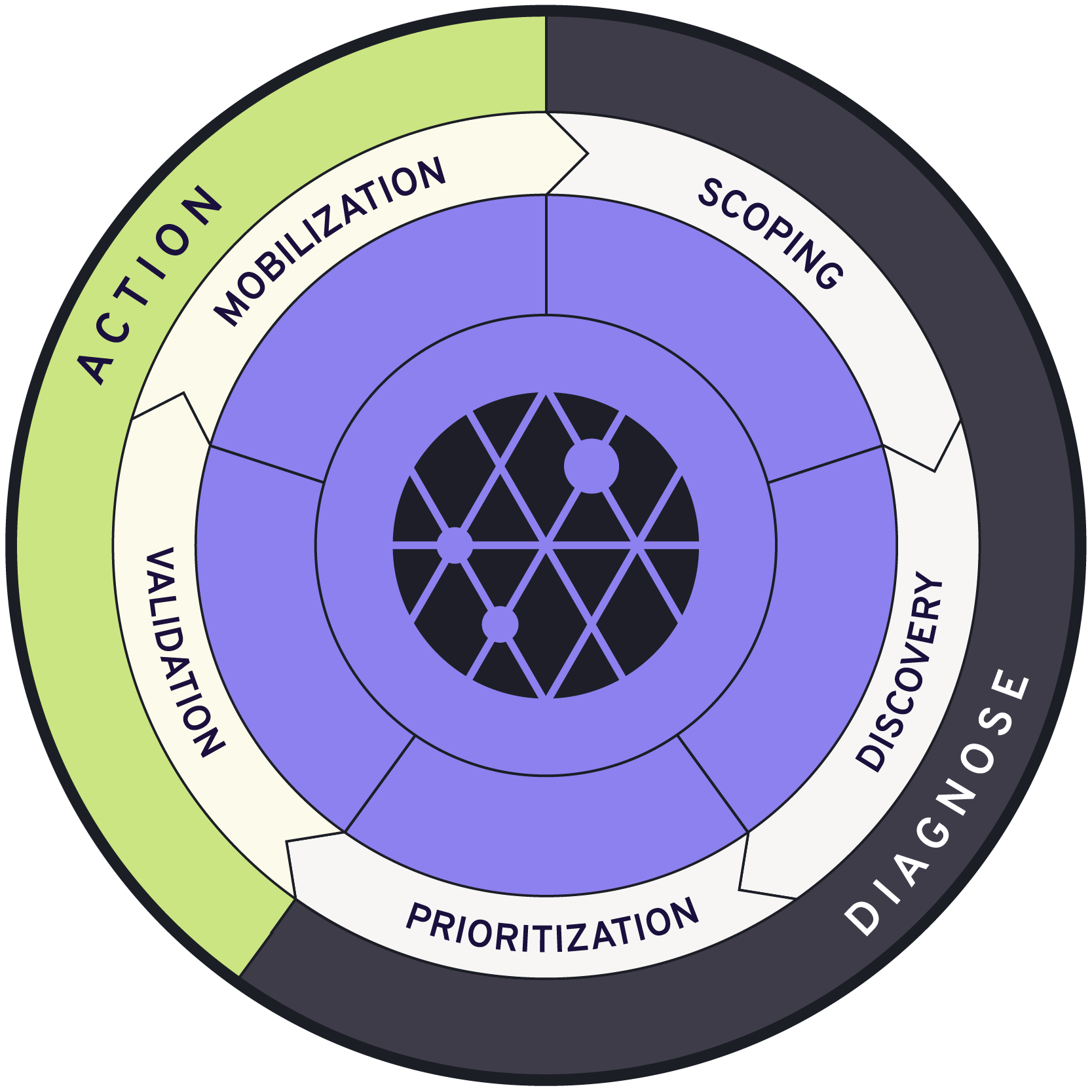
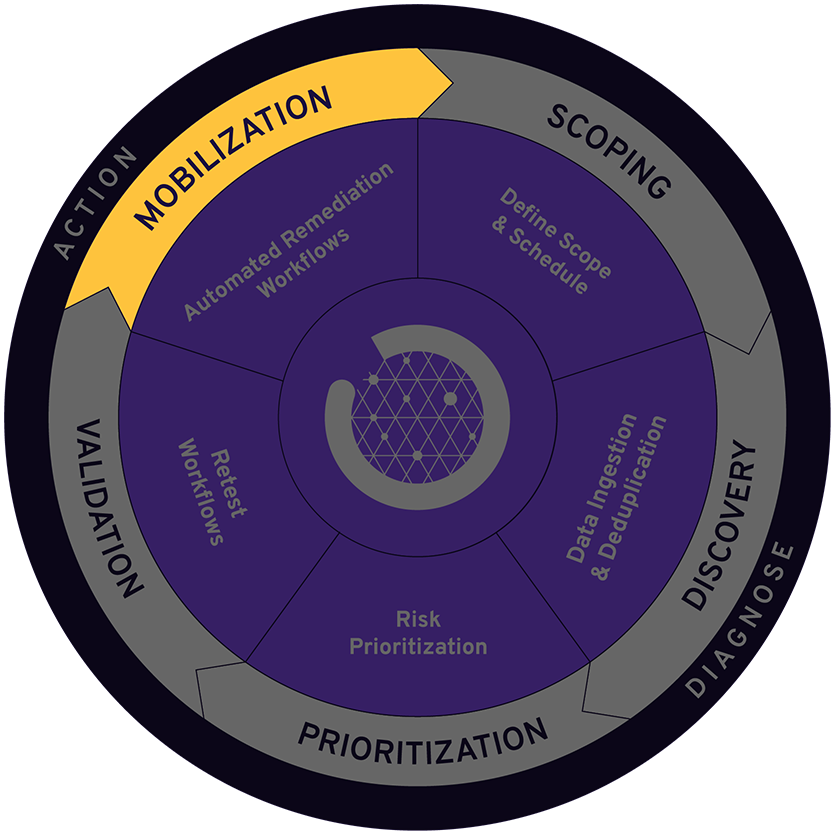
What is Scoping
Scoping sets the foundation for your CTEM program by defining which assets should be evaluated for threat exposure and how they should be prioritized based on the company’s business objectives and potential risk impact.
How PlexTrac helps
Establish clear asset ownership and manage all assets within PlexTrac for comprehensive attack surface visibility. Use this centralized view to collaborate across teams and define the testing scope based on business priorities and risk. Once the scope is established, leverage PlexTrac’s scheduling feature enables engagement management to support a continuous cadence of continuous testing
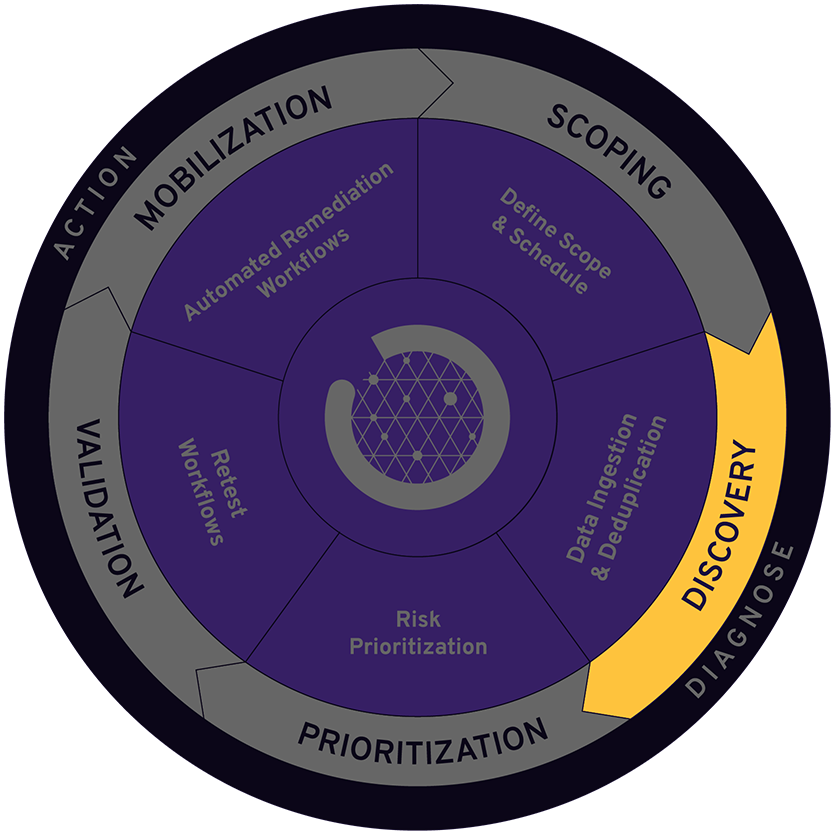
What is Discovery
Discovery is where organizations identify potential exposures within the systems and assets that are part of the scope. It involves both manual testing and automated tools to build an up-to-date view of the organization’s threat landscape to lay the groundwork for effective prioritization and validation.
How PlexTrac helps
Conduct manual testing, such as pentests, repeatable test plans, adversary emulation, or other offensive assessments, directly within PlexTrac. Consolidate these results with data from integrated discovery tools, which are automatically deduplicated to reduce noise. This enables continuous monitoring of assets and exposures within the defined scope.
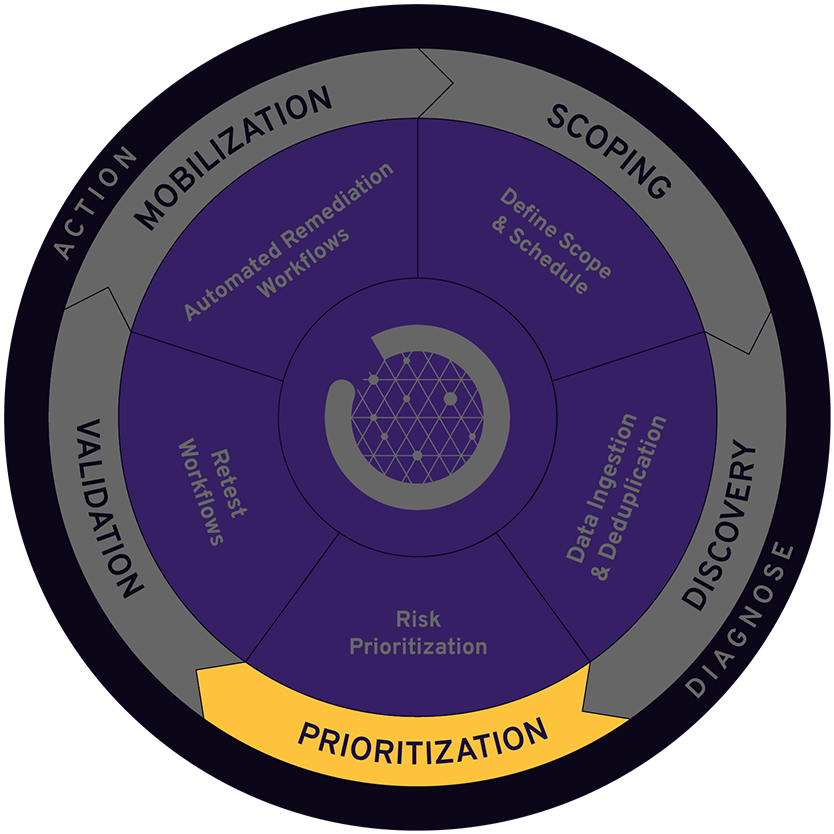
What is Prioritization
CTEM is not about remediating every exposure, but about prioritizing those that pose the greatest business risk and are most likely to be exploited. Effective risk prioritization must consider a combination of urgency, severity, compensating controls, risk appetite and overall potential impact to the organization. This ensures that resources are focused on exposures that matter most to the business.
How PlexTrac helps
Automate contextual, risk-based prioritization with fully configurable scoring equations that enrich exposures with a risk score based on potential business impact. This enables teams to identify the highest impact threats, align on treatment plans, and track remediation efforts.
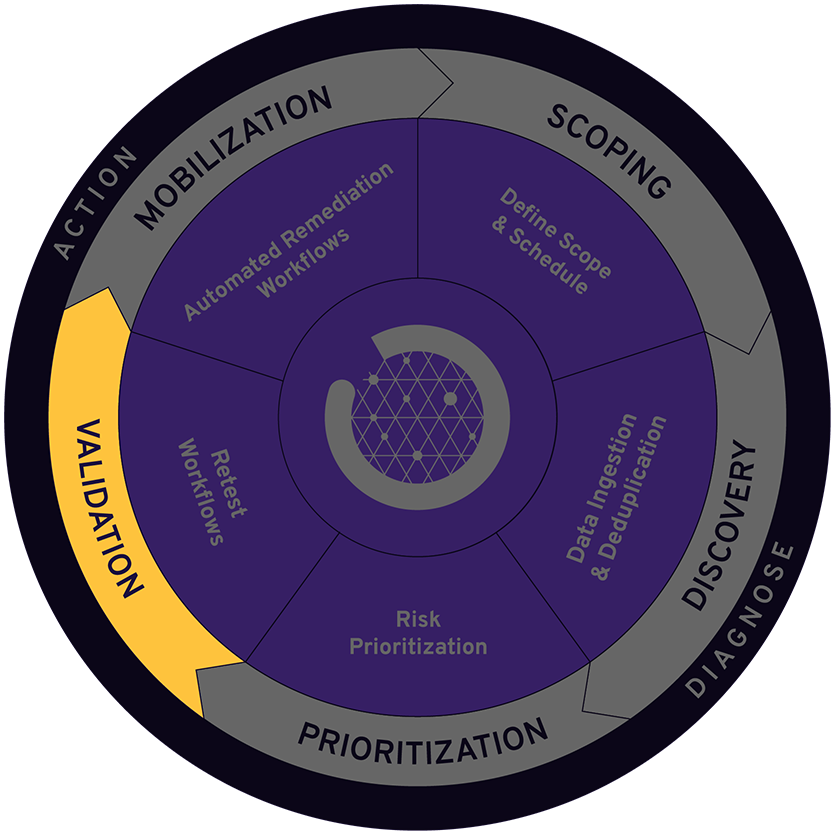
What is Validation
Validation tests how identified exposures could be exploited by attackers and how detection and response controls perform in real-world scenarios. It often involves manual assessments like penetration tests and red team exercises to evaluate likely attack success, potential business impact, and response readiness. Effective validation removes uncertainty so teams can focus on remediating exposures with proven adversarial impact.
How PlexTrac helps
Continuously validate the prioritized exposures that are scored as most critical by using automated retesting and validation workflows, ensure your security team stays focused on the highest-impact risks.
What is Mobilization
Mobilization is the process of organizing and enabling teams to act on CTEM findings by reducing friction throughout the remediation orchestration workflows. It emphasizes automation, clear communication channels, and cross-functional collaboration to reduce friction and accelerate risk reduction.
How PlexTrac helps
Mature remediation workflows by assigning, tracking, and collaborating on CTEM findings directly in PlexTrac. Integrate with ticketing systems to eliminate manual steps and enable bi-directional updates between systems that streamline collaboration. Leverage automation to reduce friction and accelerate resolution of high-priority exposures.
PlexTrac Benefits
One platform to manage assets for full attack surface visibility
Maintain full attack surface visibility and continuously monitor assets to identify findings through a wide range of integrated discovery tools and manual testing efforts.
Automatically prioritize risk from manual and automated testing
Enrich your consolidated proactive security data with contextual risk scoring to prioritize remediation based on business risk and increase actionability.
Speed mobilization with automated remediation workflows and integrated ticketing systems
Use trigger events to build automated remediation workflows that may integrate with existing security and collaboration tools like Jira and ServiceNow to speed remediation and mature workflows.
Real-time reporting and actionable insights
Drive quicker decisions and improved communication by leveraging dynamic, real-time analytics with visuals to compare trends over time and demonstrate ROI from continuous validation efforts.
Learn How to Conquer the Last Mile of Continuous Validation
Check out our demos to see just how easy it is to coordinate your continuous assessment efforts effectively and efficiently with PlexTrac to achieve measurable results.
Frequently Asked Questions About CTEM
Through continuous monitoring, evaluating, and actively mitigating security risks, continuous threat exposure management (CTEM) offers a framework to identify, prioritize, and remediate risks proactively. CTEM provides much-needed real-time visibility into vulnerabilities and threats, and empowers them to prioritize these cyber risks before they become exploitations or data breaches.
You can learn more about the importance of CTEM in this guide.
PlexTrac’s exposure assessment platform enables managed service providers and enterprises to create a continuous risk-driven approach to security that aligns with organizational objectives. Designed to support manual test data, the platform helps organizations take a proactive approach to reduce risk and advance cybersecurity maturity.
PlexTrac’s platform streamlines the continuous threat exposure management (CTEM) lifecycle by:
- Centralizing data management from exposure assessment data sources such as manual testing, pentest tools, vulnerability scanners, and attack surface management platforms to provide full attack surface visibility and make data immediately actionable
- Streamlining manual pentest reporting and automatically prioritizing remediation
- Unifying teams within a single platform for effective collaboration
- Accelerating mean-time-to-remediation by automating remediation orchestration workflows
- Preventing risk recurrence by triggering re-testing and validation
Traditional exposure assessment approaches often involve multiple, disparate tools, resulting in data silos and a limited view of your organization’s vulnerabilities. Traditional point-in-time penetration testing and vulnerability assessment tools are also often focused on reactive defensive measures and incident response, while CTEM emphasizes a proactive approach to risk management. CTEM solutions prioritize risk across all of your data sources (pentests, vulnerability management scanners, threat intelligence, etc.) to help organizations focus on the most critical issues first.
You can learn more about implementing CTEM solutions in this guide.
PlexTrac ingests and prioritizes data from vulnerability scanners, Cyber Asset Attack Surface Management (CAASM) tools, and adversarial exposure validation technologies such as Penesting as a Service (PTaaS) and Breach and Attack Simulation (BAS), helping organizations protect critical assets, reduce risk, and improve compliance. Between an extensive list of pre-built integrations and an open API, the PlexTrac platform makes it easy to unify all security data and pentest findings. Findings can also be imported directly into PlexTrac via CSV files.
You can see a list of integrations here.
Featured Resources
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Magic Quadrant is a registered trademark of Gartner, Inc. and/or its affiliates and is used herein with permission. All rights reserved.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from PlexTrac.
Gartner, Inc. Magic Quadrant for Exposure Assessment Platforms. Mitchell Schneider, Dhivya Poole, Jonathan Nunez. 10 November 2025
Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.

Get Started With PlexTrac
Jump into a demo and see PlexTrac for CTEM in action.