Exposure Assessment Platform
- What is an Exposure Assessment Platform?
- Why Are Exposure Assessment Platforms Important?
- How Does an EAP Compare to Traditional Vulnerability Management?
- Key Capabilities of Exposure Assessment Platforms
- How Does an EAP Fit Into Continuous Threat Exposure Management (CTEM)?
- Do Exposure Assessment Platforms Replace Vulnerability Scanners or Testing Tools?
- How Can PlexTrac Help with Exposure Assessment?
What is an Exposure Assessment Platform?
An Exposure Assessment Platform is a cybersecurity solution designed to continuously identify and prioritize all types of exposures (vulnerabilities, misconfigurations, identity issues and shadow assets) across an organization’s entire digital environment. These platforms act as a centralized intelligence layer for exposure management.
By integrating with vulnerability scanners, attack surface discovery tools, threat intelligence feeds and manual testing sources, an exposure assessment platform provides a single, normalized view of an organization’s attack surface. This unified perspective helps security teams understand the relationships between assets, exposures and potential attack paths, making it easier to focus remediation on the most significant risks.
Why Are Exposure Assessment Platforms Important?
Modern organizations operate in complex hybrid and multi‑cloud environments where new exposures arise continually. Traditional vulnerability management tools often rely on scheduled scans and severity scores, which provide limited context and may overlook interconnected risks. Exposure assessment platforms address these challenges by providing:
- Unified visibility across the attack surface – They build a consolidated inventory of internal and external assets, including shadow IT, cloud resources and on‑premises systems, to ensure nothing is overlooked.
- Context‑driven prioritization – By combining asset criticality, threat intelligence, business context and attack‑path analysis, these platforms rank exposures based on exploitability and potential impact. This allows teams to focus remediation efforts where they matter most.
- Mobilization and coordination – Dashboards, analytics and treatment recommendations guide remediation teams, streamline workflows and track program effectiveness.
- Continuous assessment – Automated discovery and analysis support an ongoing security posture rather than a series of point‑in‑time assessments. This helps organizations shift from reactive vulnerability management to proactive exposure management.
The end result is improved resilience, better collaboration across security operations teams, and the ability to demonstrate continuous risk reduction to stakeholders.
How Does an EAP Compare to Traditional Vulnerability Management?
Traditional vulnerability management focuses on discovering and remediating software flaws through periodic scans and high‑level severity scores. Exposure assessment platforms expand and enhance this approach in several ways:
- Broader scope – An EAP includes misconfigurations, identity exposures, shadow IT and attack‑path relationships across IT, cloud, operational technology and identity domains. Traditional vulnerability management tools generally scan only for known software vulnerabilities.
- Contextual prioritization – An EAP correlates vulnerability data with threat intelligence, asset value and exploit likelihood to prioritize remediation. Traditional tools often rely on severity ratings without full context.
- Integration and orchestration – By aggregating data from scanners, attack‑surface management tools and workflow systems, an EAP acts as the central hub for exposure management. Traditional tools typically lack this unified view.
- Continuous and proactive – Exposure assessment platforms support continuous discovery and analysis, enabling proactive risk reduction. Traditional vulnerability assessments usually run on fixed schedules and security teams react to vulnerabilities after they are discovered.
Key Capabilities of Exposure Assessment Platforms
Effective exposure assessment platforms typically provide the following capabilities:
- Asset discovery and attack‑surface management – Build a comprehensive inventory of internal and external assets, including unmanaged or rogue systems. This inventory forms the foundation of exposure management.
- Vulnerability and misconfiguration assessment – Integrate with scanners and configuration assessment tools to identify weaknesses across on‑premises, cloud and hybrid environments.
- Threat and exposure intelligence – Incorporate threat intelligence to understand exploitability, attacker techniques and emerging threats.
- Risk prioritization and analytics – Use risk scoring algorithms that consider asset criticality, exploit likelihood and business impact to rank exposures. Provide dashboards and visualizations that support data‑driven decision making.
- Attack path mapping and validation – Map relationships among assets and identities to reveal attack paths. Some platforms also provide validation through simulations or testing to confirm which exposures are real threats.
- Workflow automation and remediation orchestration – Integrate with ticketing and collaboration tools to automate remediation workflows, assign tasks and track progress.
- Reporting and compliance support – Generate reports and metrics that translate technical exposures into business‑risk terms to satisfy stakeholders and regulatory requirements.
How Does an EAP Fit Into Continuous Threat Exposure Management (CTEM)?
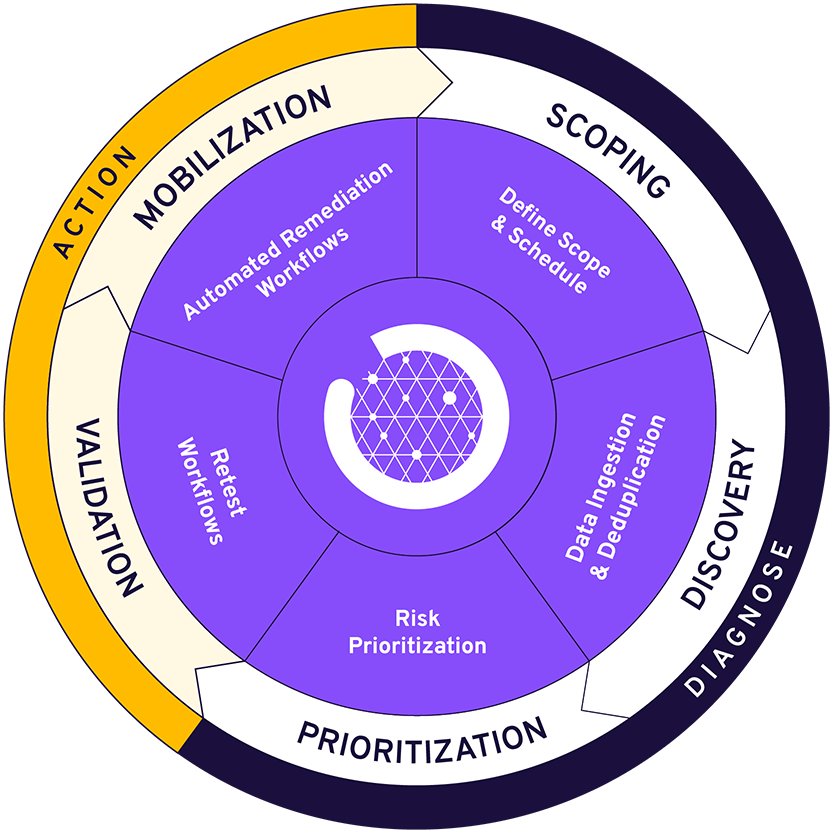
Continuous Threat Exposure Management (CTEM) is an iterative framework that helps organizations continuously identify, prioritize, validate and remediate exposures. The CTEM lifecycle consists of five phases:
- Scoping – Define and prioritize the systems, applications and business processes to include in an exposure management program.
- Discovery – Continuously identify assets, vulnerabilities, misconfigurations and identity exposures across the environment.
- Prioritization – Rank exposures by exploitability and potential business impact so remediation efforts target the most critical risks.
- Validation – Confirm which exposures are real threats through testing or simulation and verify that remediation reduces risk.
- Mobilization – Coordinate and automate remediation across teams, monitor progress and communicate improvements.
Exposure assessment platforms underpin discovery, prioritization and mobilization. They provide the unified visibility, analytics and workflow automation needed to support an effective CTEM program.
Do Exposure Assessment Platforms Replace Vulnerability Scanners or Testing Tools?
No. Exposure assessment platforms do not replace scanners or other security tools. Instead, they ingest, normalize and deduplicate data from a variety of sources, including vulnerability scanners, penetration tests, configuration assessments, threat intelligence feeds, attack surface management platforms and manual testing. By unifying this data into a single platform, EAPs provide a comprehensive view of exposures and apply consistent risk scoring and reporting. This enables teams to analyze, collaborate on and track remediation across every exposure, regardless of its origin.
How Can PlexTrac Help with Exposure Assessment?
PlexTrac has evolved from a pentest reporting tool into a comprehensive exposure assessment platform. It consolidates data from pentest tools, scanners and manual assessments to centralize exposure management in one place. Key capabilities include:
- Centralized data ingestion and deduplication – PlexTrac aggregates findings from multiple sources, removes duplicates and creates a single source of truth.
- AI‑assisted reporting and speed – Automation and AI accelerate report writing, with pre‑built findings, customizable templates and automatically generated remediation recommendations.
- Contextual risk scoring and prioritization – Configurable risk equations enrich findings with business context to focus remediation on the most critical threats.
- Workflow automation and remediation orchestration – Integrated ticketing and rule‑based workflows help teams automate remediation tasks and track mobilization progress.
- CTEM lifecycle support – PlexTrac supports each phase of the CTEM lifecycle: scoping engagements through flexible scheduling, discovering assets with integrated tools, prioritizing using contextual scoring, validating remediation through retest workflows and mobilizing teams via ticketing integrations.
- Dashboards and analytics – Dynamic dashboards provide real‑time visibility into findings and asset data, enabling organizations to track progress and demonstrate risk reduction over time.
By serving as the control center for collecting, analyzing and prioritizing exposure data and orchestrating remediation workflows, PlexTrac helps organizations mature their exposure management and CTEM programs and reduce overall risk.